Concept Of Network Hacking and Tools Used
|
|
Network Hacking generally means gathering information about domain by using tools like Telnet, NslookUp, Ping, Tracert, Netstat etc. It also includes OS Fingerprinting, Port Scanning and Port Surfing using various tools. Therefore, Below I am telling about 4 tools with their definition along with example to clarify things b/w you.
1. Ping :- Ping is part of ICMP (Internet Control Message Protocol) which is used to troubleshoot TCP/IP networks. So, Ping is basically a command that allows you to check whether the host is alive or not.
To ping a particular host the syntax is (at command prompt)--
c:/>ping hostname.com
example:- c:/>ping www.google.com
2. Netstat :- It displays protocol statistics and current TCP/IP network connections. i.e. local address, remote address, port number, etc.
It's syntax is (at command prompt)--
c:/>netstat -n
3. Telnet :- Telnet is a program which runs on TCP/IP. Using it we can connect to the remote computer on particular port. When connected it grabs the daemon running on that port.
The basic syntax of Telnet is (at command prompt)--
c:/>telnet hostname.com
By default telnet connects to port 23 of remote computer.
So, the complete syntax is-
c:/>telnet www.hostname.com port
example:- c:/>telnet www.yahoo.com 21 or c:/>telnet 192.168.0.5 21
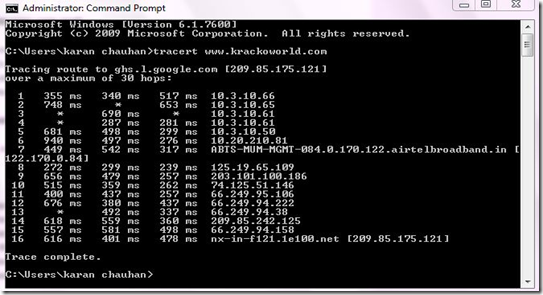
4. Tracert :- It is used to trace out the route taken by the certain information i.e. data packets from source to destination.
It's syntax is (at command prompt)--
c:/>tracert www.hostname.com
example:- c:/>tracert www.krackoworld.com
Here "* * * Request timed out." indicates that firewall installed on that system block the request and hence we can't obtain it's IP address.
various attributes used with tracert command and their usage can be viewed by just typing c:/>tracert at the command prompt.
The information obtained by using tracert command can be further used to find out exact operating system running on target system and much more.
That’s it! This chapter is over…
Join me on Google+
|
|
Respected Readers :-
|

E njoyed this post very much – So why not you Subscribe to our regular Email Updates ! and stay connected with us forever .
















0 comments :
Your feedback is always Precious to us.
I will try to answer all the queries as soon as possible.
Regards
karan chauhan